Limited Time Offer!
For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly.
Master DevOps, SRE, DevSecOps Skills!
Job Overview:
We are looking to add a talented DevSecOps Engineer to our vibrant team. The ideal applicant will have a solid history in security-focused DevOps processes. In order to guarantee the security of our infrastructure and apps throughout the development lifecycle, it will be your responsibility to include security procedures into the DevOps pipeline.
Key Responsibilities:
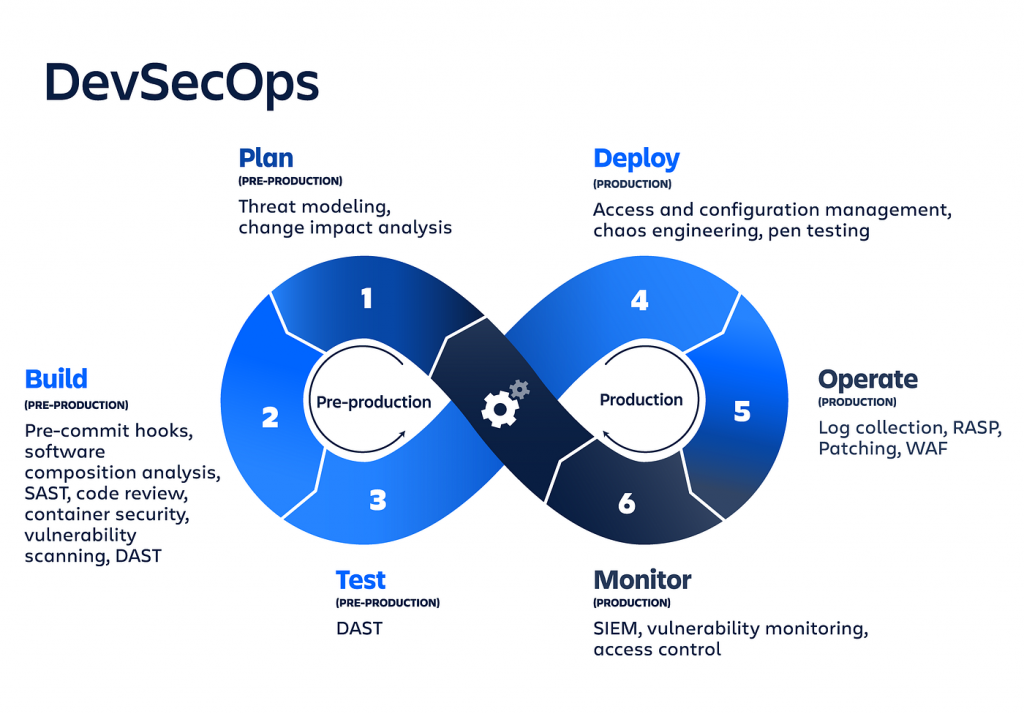
Security Integration: To guarantee safe software delivery, include security controls into CI/CD pipelines.
Integrating security measures into CI/CD pipelines is the main duty of a DevSecOps engineer. To stop vulnerabilities from entering the production environment, this entails making sure that security checks are automated and integrated into the software delivery process.
- Integrate security practices within CI/CD pipelines.
- Ensure secure software delivery processes.
Infrastructure Security: Maintain and safeguard cloud infrastructure while adhering to best practices and industry standards.
Cloud infrastructure management and security are a vital component of the job. DevSecOps Engineers guard the company against any security risks by making ensuring the infrastructure conforms with industry standards and best practices.
- Control and safeguard cloud computing infrastructure.
- Make ensuring that best practices and industry standards are followed.
Automation: Create and manage procedures and tools for automated security testing.
It is crucial to create and manage automated security testing procedures and technologies. Automation makes ensuring that security tests are regularly implemented at every level of development and deployment, which aids in the early discovery of security concerns.
- Create and manage automated security testing procedures and tools.
- Automate tasks to improve security protocols.
Monitoring and Incident Handling: Establish and oversee security monitoring frameworks and address security-related issues.
Another vital duty is to set up and maintain security monitoring systems. DevSecOps Engineers need to be ready to react to security issues quickly and effectively to minimize the damage to the company.
- Install and oversee security surveillance systems.
- React as soon as possible and effectively to security incidents.
Cooperation: To guarantee a cohesive approach to security, work closely with the development, operations, and security teams.
Working together is essential in the DevSecOps position. To guarantee a consistent approach to security, engineers collaborate closely with the development, operations, and security teams. Embracing security measures into all teams requires effective communication and coordination.
- Collaborate closely with the security, operations, and development teams.
- Make sure that every team has the same security strategy.
Compliance: Verify that systems abide with all applicable laws, rules, and guidelines, including GDPR, HIPAA, etc.
A basic duty is to make sure that systems abide with applicable laws and guidelines, such GDPR and HIPAA. DevSecOps Engineers make sure the company complies with legal and regulatory obligations by maintaining compliance paperwork and processes.
- Verify that systems adhere to all applicable laws and guidelines (e.g., GDPR, HIPAA).
- Preserve processes and documents related to compliance.
Vulnerability Management: Oversee repair activities and do routine vulnerability assessments.
Upholding a safe environment requires coordinating repair activities and doing frequent vulnerability assessments. Vulnerabilities are found and fixed by DevSecOps Engineers before they may be exploited.
- Make vulnerability assessments on a regular basis.
- Oversee remediation activities to resolve vulnerabilities.
Documentation: Keep thorough records of all security incidents, rules, and procedures.
It is essential to keep thorough records of all security occurrences, rules, and procedures. All stakeholders may view and understand security procedures thanks to current documentation.
- Keep thorough records of all occurrences, policies, and processes related to security.
- Make sure that all security documentation is current and easily available.
Required Skills and Qualifications:
Education: Bachelor’s degree in information technology, computer science, or a similar discipline.
Usually, one needs a bachelor’s degree in computer science, information technology, or a similar discipline. The information and abilities required for the position are provided by this educational foundation.
Experience: Three years or more in security and DevOps positions.
It’s common to need at least three years of experience in security and DevOps jobs. Understanding the challenges of incorporating security into the DevOps framework is made easier by this experience.
Technical Skills:
- proficiency with AWS, Azure, and GCP cloud platforms.
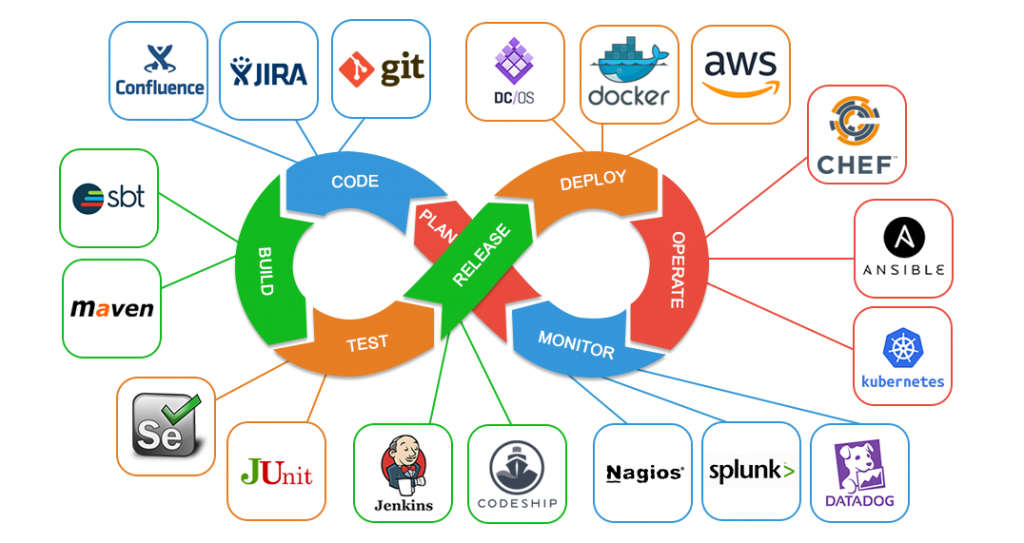
- solid familiarity with CI/CD technologies (CircleCI, Jenkins, GitLab).
- familiarity with orchestration and containerization (Docker, Kubernetes).
- familiarity with security procedures and technologies (OWASP, SAST, DAST, IAST).
- knowledge of infrastructure as code (using Ansible or Terraform).
Soft Skills:
- exceptional ability to solve problems.
- strong teamwork and communication skills.
- meticulous and committed to ongoing development.
Preferred Skills and Certifications:
- Credentials: It is quite desired to have relevant security certifications like OSCP, CEH, and CISSP. These credentials show a professional’s proficiency and dedication to security.
- Experience: It is helpful to have previous experience in a fast-paced, comparable function. It offers useful information and perspectives that are applicable to the DevSecOps position.
- Knowledge: It’s critical to comprehend industry norms and legal obligations. This information guarantees the organization’s continued compliance and security.
Benefits and Compensation
Competitive Salary :- Offering a market-competitive compensation plan is customary in order to draw and keep top talent.
Benefits :- Benefits including comprehensive dental, vision, and health insurance are typical. These perks contribute to workers’ wellbeing.
Professional Growth:- There are chances for job progression and further education. Employers make growth investments in their staff in order to promote an innovative and high-achieving culture.
Work Environment:- It’s critical to have an inventive and cooperative work culture. It propels the company ahead by fostering innovation and cooperation.

