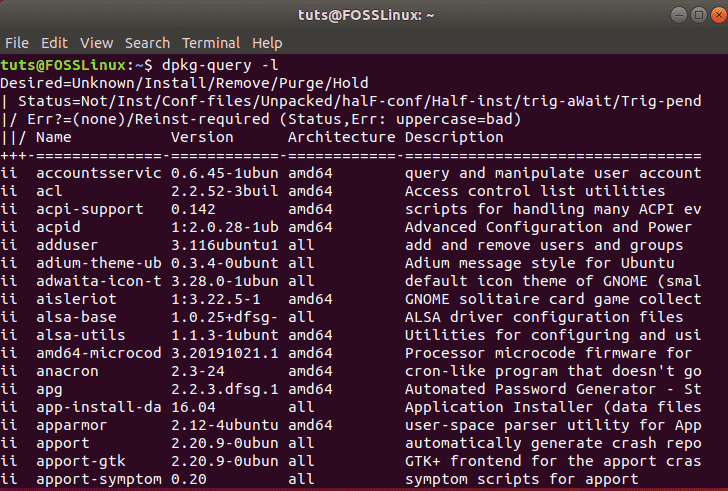
The dpkg-query command is used in Debian-based Linux distributions (like Ubuntu, Debian, Kali Linux) to query the dpkg database for information about installed packages. It is useful when you need to check package details, file locations, or dependencies. Unlike dpkg, which is mainly used for installing or removing packages, dpkg-query is purely for querying the…
Top 10 Commands with explanation of “dpkg” command
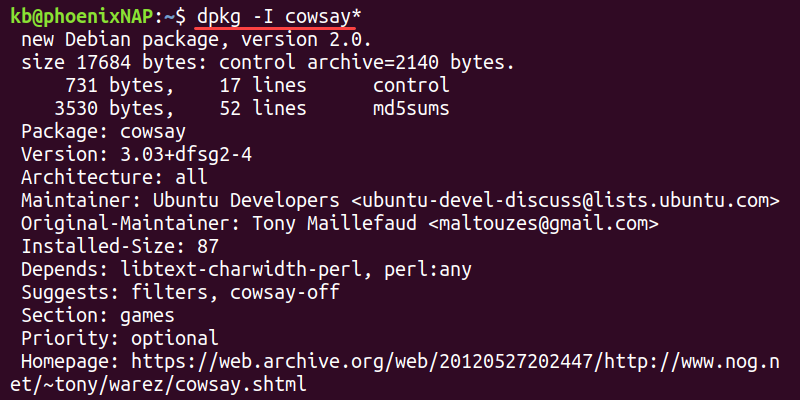
The dpkg (Debian Package Manager) command is used in Debian-based Linux distributions (such as Ubuntu, Debian, and Kali Linux) for installing, removing, and managing .deb packages. Unlike apt, dpkg does not resolve dependencies automatically but provides more low-level package control. 1. Install a .deb Package ✔ What it does: 📌 Example: 📌 If dependencies are…

How to Configure Facebook Page profile. Step by Step Guide
In today’s digital world, having a well-optimized Facebook Page is crucial for businesses, influencers, and communities. Whether you’re launching a brand, promoting a service, or building a community, a properly set-up Facebook Page helps you connect with your audience effectively. If you’re unsure where to start, don’t worry! This step-by-step guide will walk you through…
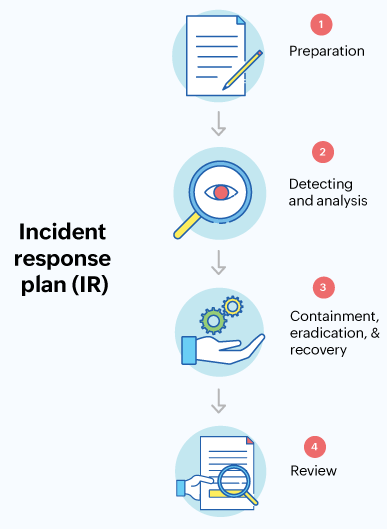
What is Incident Response (IR) Tools?
What are Incident Response (IR) Tools? Let’s start with the basics. Imagine your organization is a fortress, and cyber threats are like intruders trying to break in. Incident Response (IR) tools are your defense systems — think of them as a team of highly skilled security guards equipped with alarms, surveillance, and protocols to handle…
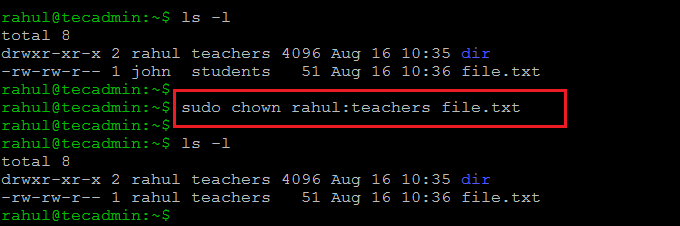
Top 10 Commands with explanation of “chown” command
The chown (Change Owner) command in Linux is used to change the owner and group ownership of files and directories. It is particularly useful when managing permissions for multiple users on a system. Every file in Linux has an owner and a group, as seen in the ls -l output: Now, let’s explore 10 powerful…

What Are Security Auditing Tools?
What Are Security Auditing Tools? Security Auditing Tools are like a security guard for your digital world. Think of them as specialized tools designed to inspect your computer systems, networks, applications, and even cloud environments for any weaknesses or vulnerabilities. Just as you might lock the doors and windows of your house to protect against…
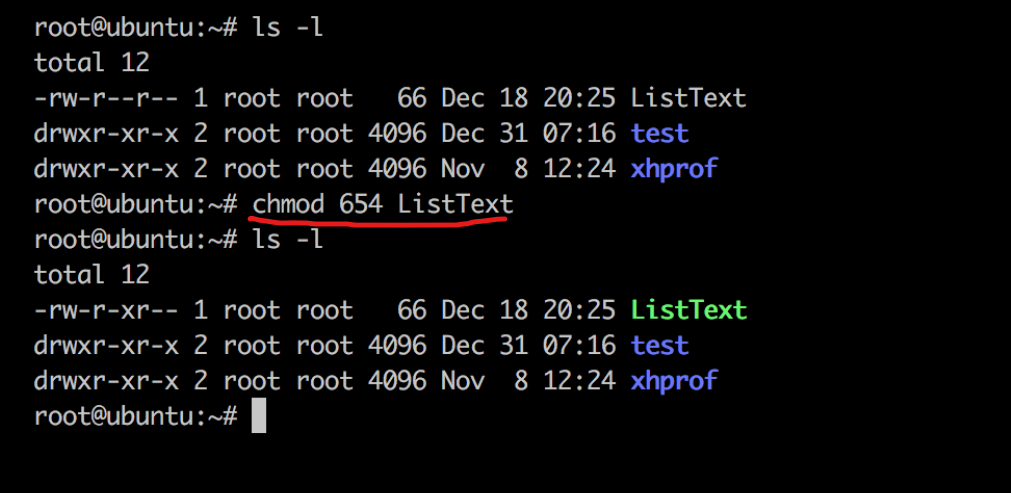
Top 10 Commands with explanation of “chmod” command
The chmod (Change Mode) command is used in Linux to modify file and directory permissions. It controls who can read (r), write (w), and execute (x) a file or directory. Understanding Permissions in Linux Each file and directory in Linux has three types of users: Each file has permission settings like: Now, let’s explore 10…
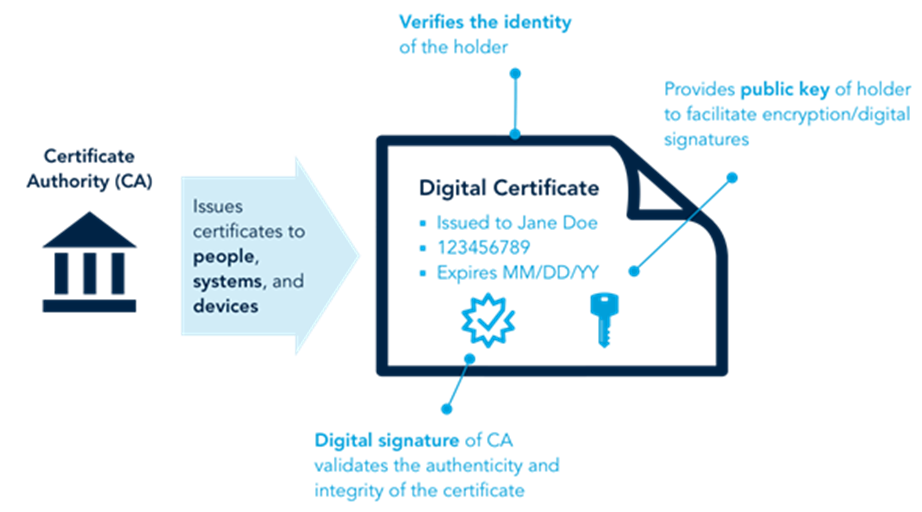
What is Digital Certificates?
What is a Digital Certificate? A Digital Certificate is an electronic document that validates the identity of an individual, organization, or device and binds it to a pair of cryptographic keys (public and private keys). It operates as a digital passport that helps establish trust in online interactions. Key components of a digital certificate include:…
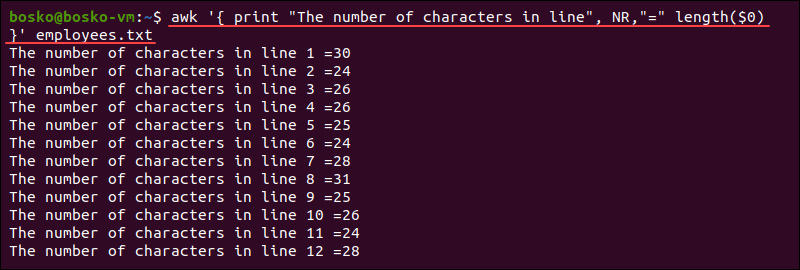
Top 20 Commands with explanation of “awk” command
The awk command in Linux is a powerful text-processing tool used for pattern scanning, extracting, formatting, and manipulating text files, logs, CSVs, and structured data. It reads files line by line, splits them into fields, and performs actions on them. Let’s go deep into 20 powerful awk commands, explained in a humanized and detailed way….

What is Encryption Tools?
What is Encryption? Encryption is the process of converting information or data into a coded format to prevent unauthorized access. This process involves using mathematical algorithms to scramble readable data (plaintext) into an unreadable format (ciphertext). Only authorized parties, who possess the correct decryption key or password, can transform the ciphertext back into its original,…