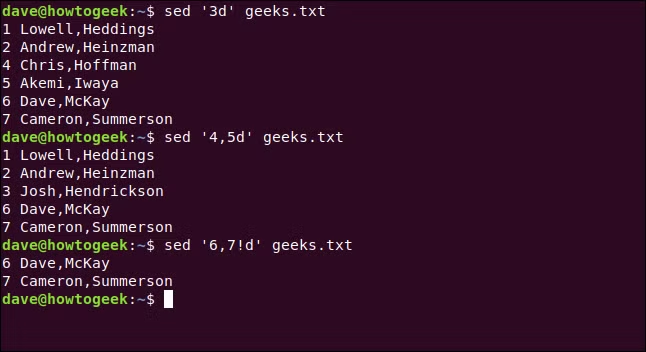
The sed (Stream Editor) command is a powerful Linux tool used for text processing. It allows for text substitution, deletion, insertion, and more, directly from the command line. This command is widely used in shell scripting, automation, and data manipulation tasks. Here is a detailed, humanized, and well-explained list of the top 20 sed commands:…

DeepSeek-V3 vs. ChatGPT: A Tale of Two AI Assistants – Who’s Right for You?
In the world of artificial intelligence, there’s a lot of buzz around AI assistants like DeepSeek-V3 and ChatGPT. Both are incredibly smart, capable, and designed to make our lives easier. But here’s the thing: they’re not the same. Think of them as two chefs in a global kitchen—one specializes in local cuisine, while the other…

DeepSeek is just a copy of open ai chatgpt or not?
Is DeepSeek Just a Copy of OpenAI’s ChatGPT? A Detailed Analysis With the rapid rise of DeepSeek, many are questioning whether it is merely a copy of OpenAI’s ChatGPT or a genuine innovation in AI technology. While there are similarities between the two, DeepSeek has distinct advantages and innovations that set it apart. 1. Different…
How DevOps Transformations Drive Business Success – Real-World Case Studies
In today’s technology-driven world, businesses constantly face pressure to innovate, deliver faster, and maintain high-quality digital services. Traditional software development and IT operations often struggle with slow release cycles, security vulnerabilities, and inefficiencies that can hinder growth. This is where DevOps steps in as a game-changer. By integrating development and operations, DevOps transformation helps organizations…
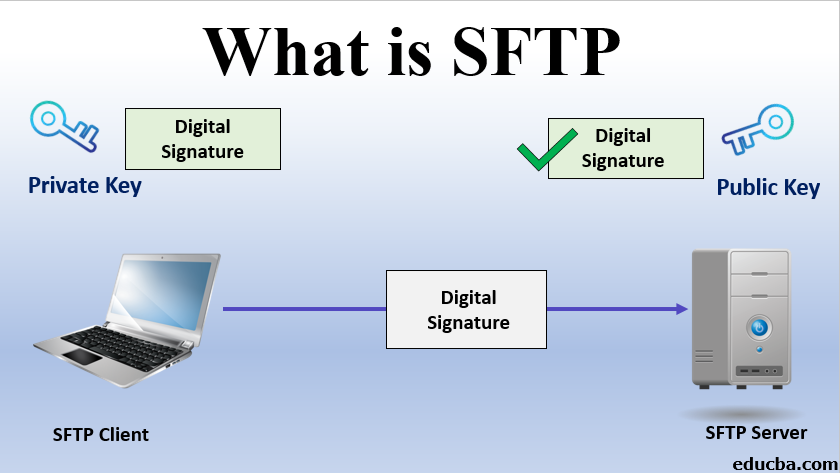
What is Secure File Transfer Protocol (SFTP) Tools
What is SFTP? SFTP (Secure File Transfer Protocol) is a secure network protocol that facilitates the transfer and management of files over a reliable data stream. Unlike traditional FTP, SFTP operates within the Secure Shell (SSH) protocol to provide a secure connection. This ensures that all data exchanged between the client and the server is…
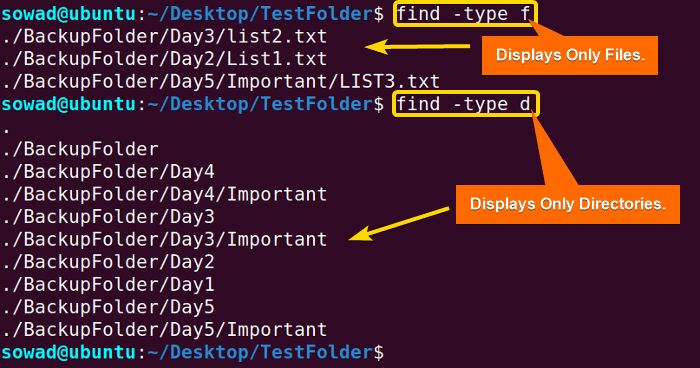
Top 20 Commands with explanation of “find” command
The find command in Linux is a powerful tool used for searching files and directories based on different criteria such as name, size, type, modification date, permissions, and more. It is one of the most frequently used commands by system administrators and DevOps engineers. Here’s an in-depth look at the top 20 find command examples…
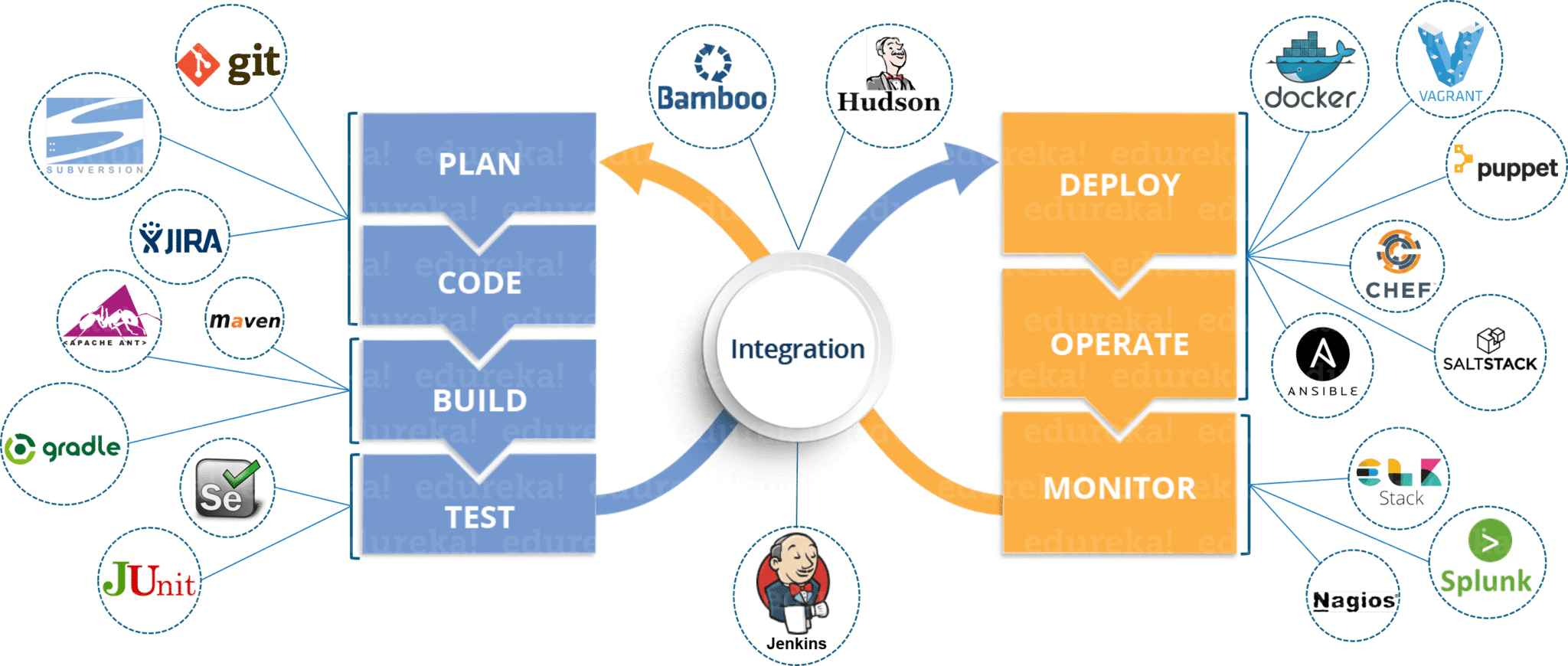
The Ultimate DevOps Tools Comparison: Choosing the Best for Your Workflow
In today’s fast-paced tech landscape, software development teams constantly strive for efficiency, speed, and reliability. DevOps has revolutionized the way organizations develop, deploy, and manage applications, making the choice of DevOps tools a critical decision. Whether you’re a startup looking to streamline deployments or an enterprise managing complex infrastructures, selecting the right DevOps tool can…
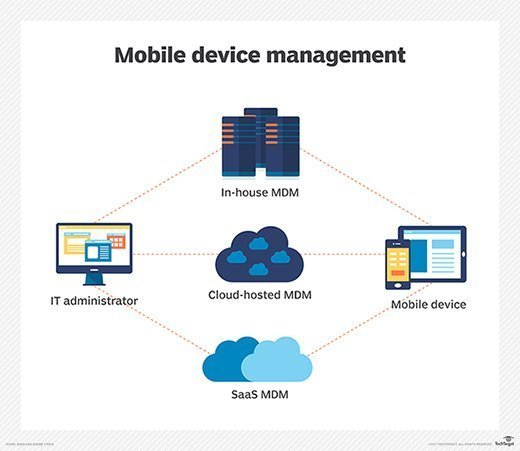
What is Mobile Device Management (MDM) Tools?
What is MDM? Mobile Device Management (MDM) refers to the suite of technologies, tools, and processes designed to help organizations effectively manage, monitor, and secure mobile devices like smartphones, tablets, laptops, and other endpoints that employees use for work purposes. These tools allow IT administrators to control and secure the usage of mobile devices, ensuring…
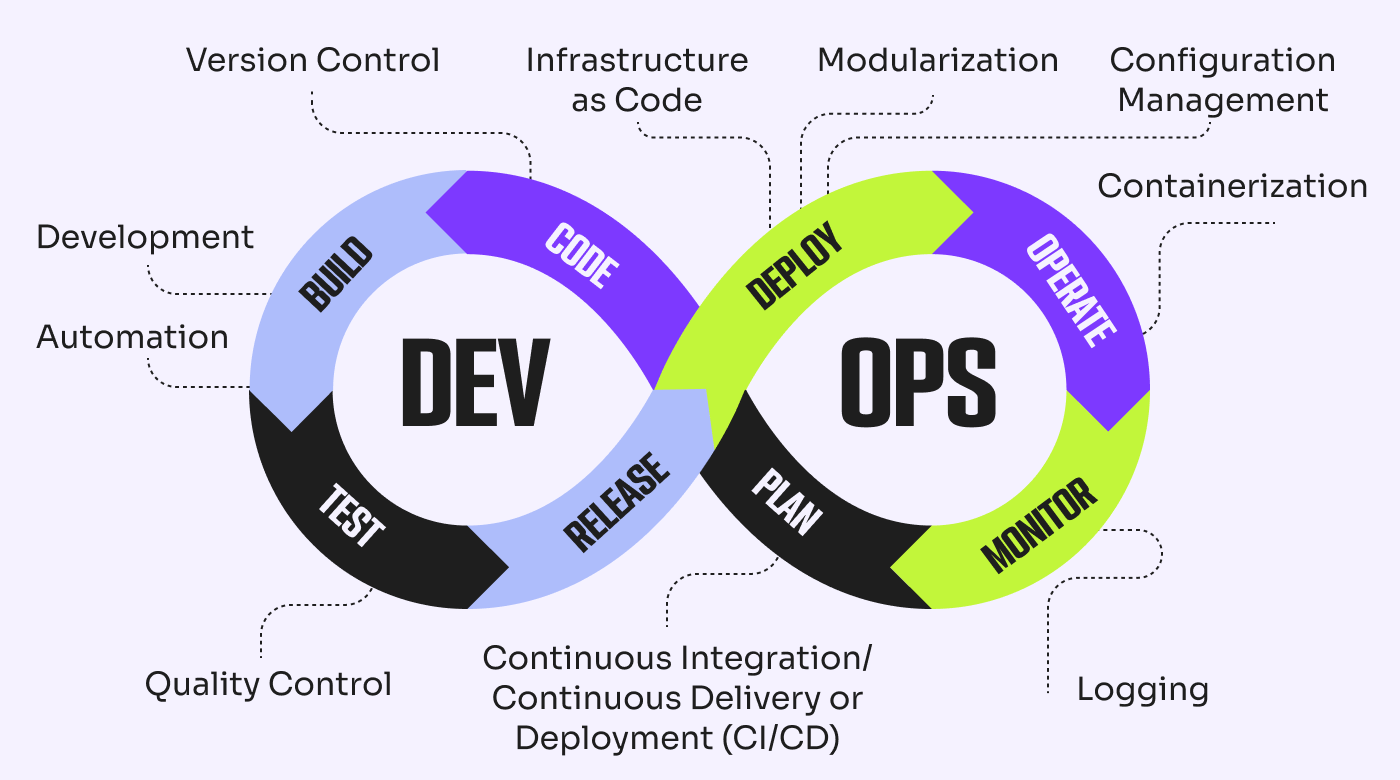
Essential DevOps Practices for High-Performance Software Delivery
In today’s fast-paced digital world, businesses must deliver software quickly, reliably, and securely. This is where DevOps comes in—a culture and set of practices that bridge the gap between development and IT operations to streamline workflows and accelerate releases. However, simply adopting DevOps is not enough; organizations must implement the right DevOps practices to truly…

What is Endpoint Security Tools?
What is Endpoint Security? Endpoint security refers to the practice of protecting network endpoints — such as desktops, laptops, mobile devices, servers, and other internet-connected devices — from cyber threats. Endpoints serve as entry points to an organization’s network and are often targeted by attackers to exploit vulnerabilities and gain unauthorized access. Endpoint security tools…