Imagine a bustling city where law enforcement and emergency services work seamlessly together to prevent crime, respond to threats, and keep people safe. Now, think of your organization’s IT infrastructure as that city, and cybersecurity threats as criminals constantly looking for vulnerabilities to exploit. SecOps (Security Operations) acts as the security force of your digital…
How to Configure Youtube Channel for Business. Step by Step Guide
YouTube is one of the most powerful platforms for businesses today. Whether you want to showcase your expertise, promote your products, or engage with potential customers, having a professional YouTube channel can be a game-changer. With over two billion active users, YouTube offers a huge opportunity to grow your brand and connect with your audience…
How to Configure X Profile for Business. Step by Step Guide
X, formerly known as Twitter, is one of the best platforms for businesses to connect with customers, grow their brand, and engage in meaningful conversations. Whether you’re a startup, small business, or an established brand, X can help you build credibility, drive traffic to your website, and create a loyal audience. If you’re looking to…

What is Security Analytics Tools?
What is Security Analytics Tools? Security Analytics Tools are advanced software solutions designed to monitor, analyze, and interpret security-related data to detect, investigate, and respond to threats and vulnerabilities within an organization’s IT infrastructure. These tools leverage technologies like big data analytics, machine learning, and artificial intelligence to provide actionable insights and help organizations maintain…
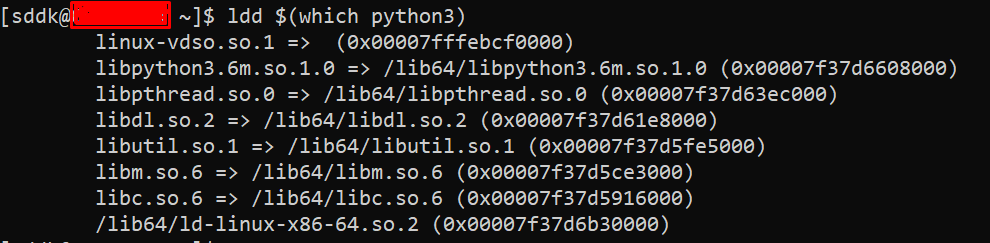
Top 10 Commands with explanation of “ldd” command
The ldd (List Dynamic Dependencies) command in Linux is used to display shared library dependencies of an executable or a shared object (.so file). It helps in debugging missing dependencies, checking linked libraries, and troubleshooting runtime issues. 1. Check Shared Libraries for an Executable ✔ What it does: 📌 Example Output: 💡 Useful for checking…
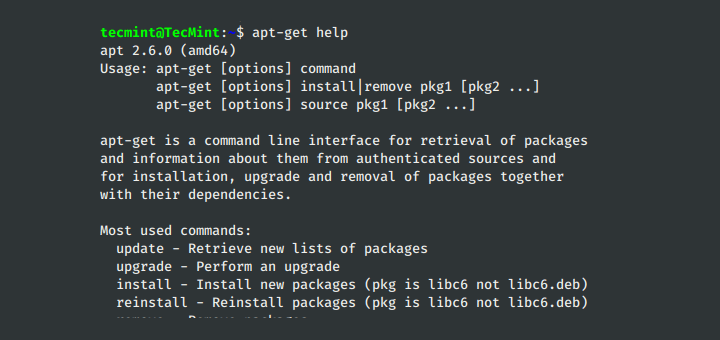
Top 10 Commands with explanation of “apt-get” command
The apt-get command is a powerful package management tool in Debian-based Linux distributions like Ubuntu, Debian, and Kali Linux. It allows users to install, update, upgrade, remove, and manage packages efficiently. Unlike dpkg, which only installs .deb files without resolving dependencies, apt-get automatically handles dependencies, making it a preferred package manager for most users. Let’s…
How to Configure Instagram Profile for Business. Step by Step Guide
Instagram is one of the best platforms for businesses today. Whether you’re a small business owner, freelancer, or entrepreneur, having a professional Instagram presence helps you connect with your audience, promote your brand, and even drive sales. If you’re wondering how to set up an Instagram Business profile, don’t worry—this guide will walk you through…
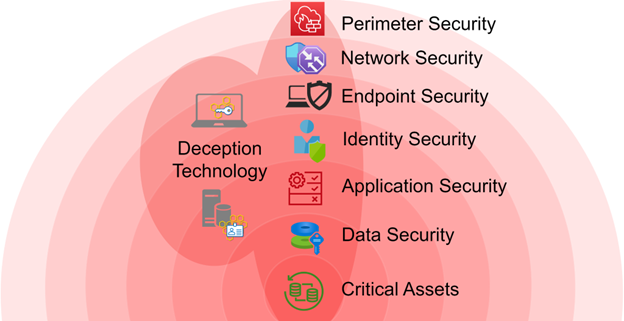
What is Deception Technology?
What is Deception Technology? Deception Technology is a cutting-edge approach to cybersecurity that employs fake systems, data, and services to confuse and trap attackers. These decoys, often indistinguishable from real systems, are designed to mislead malicious actors into revealing their presence and intent. Once attackers interact with these traps, security teams are alerted, enabling them…
How to Configure Facebook group. Step by Step Guide
Creating a Facebook Group is a great way to build a community, whether for your business, interests, or social causes. The best part? It’s completely free and allows you to engage with people who share similar interests. Step 1: Creating Your Facebook Group 1.1 Log Into Facebook First, go to Facebook and log in to…

What is Cyber Threat Intelligence (CTI) Tools?
What is Cyber Threat Intelligence (CTI) Tools? Cyber Threat Intelligence (CTI) tools are like the superheroes of the cybersecurity world. They are specially designed platforms or software solutions that help organizations gather, analyze, and act on critical information about cyber threats. These tools take raw data—from open-source intelligence (OSINT), internal logs, dark web activities, and…

