Limited Time Offer! For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly. Master DevOps, SRE, DevSecOps Skills! Enroll Now Having analyzed Bangalore Orbit’s website (https://www.bangaloreorbit.com/), I’ve crafted a compelling piece highlighting their products and services. This content emphasizes the curated and personalized approach they offer to explore Bengaluru’s…
Month: July 2024
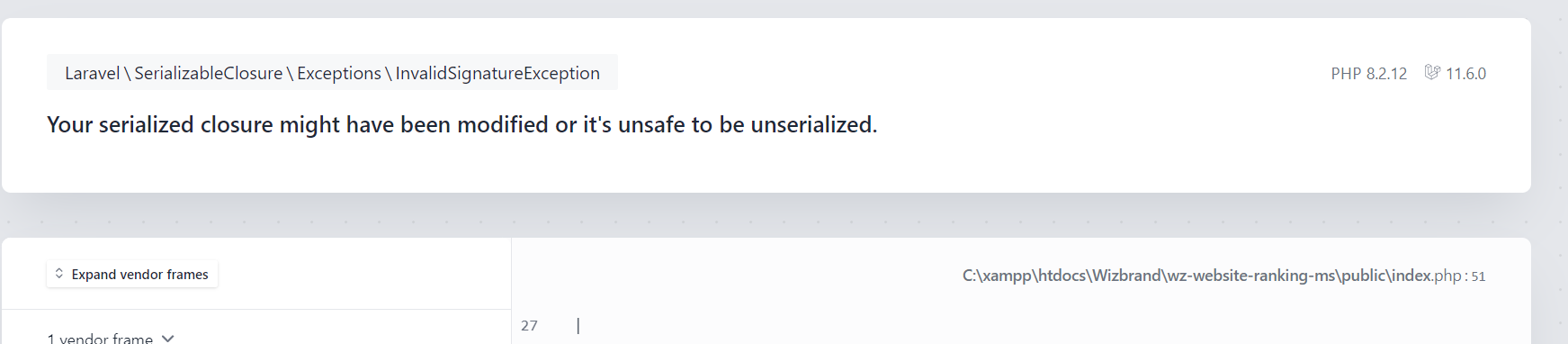
Laravel Error: Your serialized closure might have been modified or it’s unsafe to be unserialized.
Limited Time Offer! For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly. Master DevOps, SRE, DevSecOps Skills! Enroll Now Step 1 :- Go to your Project Terminal. Step 2:- Run the following command one by one and your issue will be solved.

Laptop Processor Suffixes Decoded: Choose the Right One for Your Needs
Limited Time Offer! For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly. Master DevOps, SRE, DevSecOps Skills! Enroll Now The letters at the end of a laptop processor’s model number typically indicate the processor’s performance characteristics and target usage. Here’s a detailed breakdown of common suffixes: Intel Processor…
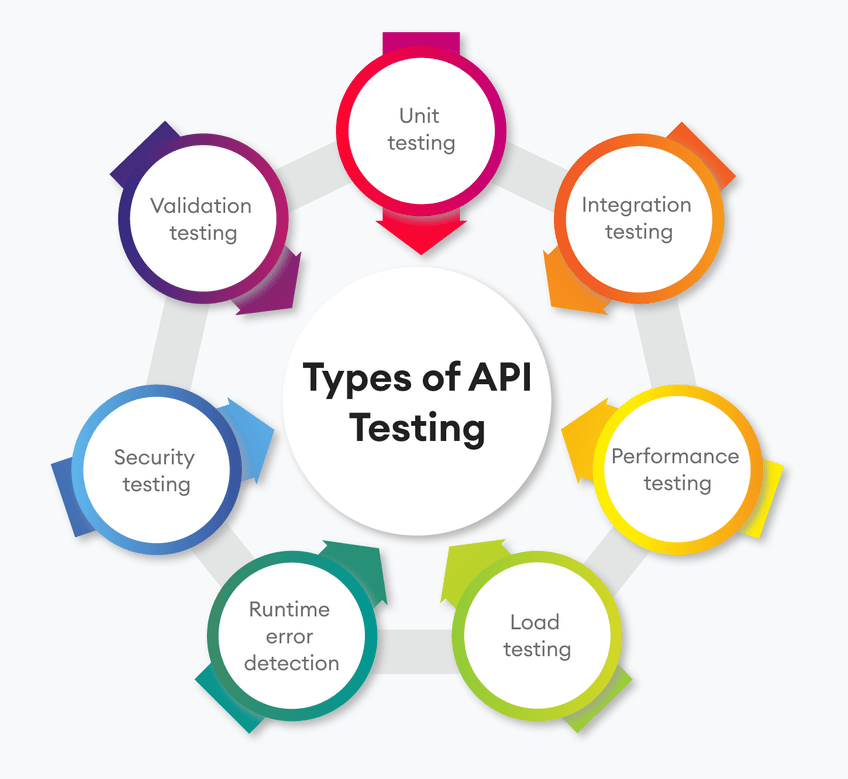
9 Essential Types of API Testing: A Comprehensive Guide to Ensure Secure and Reliable APIs
Limited Time Offer! For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly. Master DevOps, SRE, DevSecOps Skills! Enroll Now Introduction to API Testing APIs, or application programming interfaces, are now essential for smooth communication between various software systems in today’s digital environment. Ensuring the dependability, security, and performance…
Measuring the Impact of DevOps Consulting on Your Business
Limited Time Offer! For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly. Master DevOps, SRE, DevSecOps Skills! Enroll Now The adoption of DevOps practices has become essential for organizations aiming to enhance operational efficiency, accelerate innovation, and achieve a competitive edge. Engaging with a DevOps consulting company can…
What is the difference between chatgpt 3.5, 4 and 4o?
Limited Time Offer! For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly. Master DevOps, SRE, DevSecOps Skills! Enroll Now The various ChatGPT versions—3.5, 4, and 4-turbo, sometimes known as 4o—represent improvements to the design and functionalities of the device. Below is a quick summary of the variations: ChatGPT…
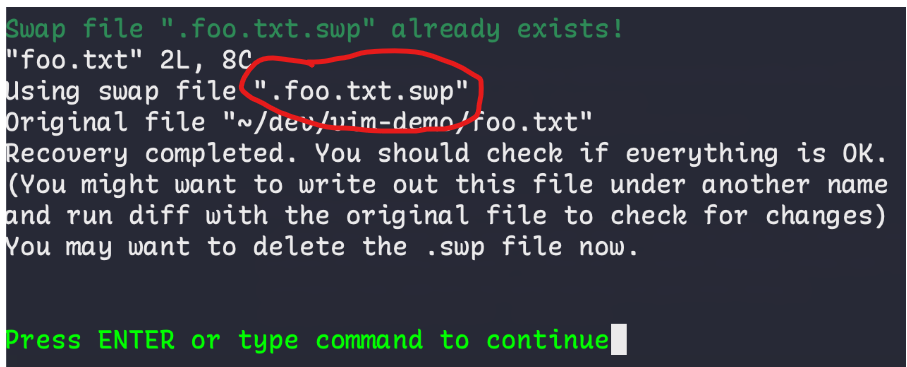
What is .swp file extension in linux?
Limited Time Offer! For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly. Master DevOps, SRE, DevSecOps Skills! Enroll Now Under Linux, swap files made with the vi or vim text editors are identified by the .swp extension. In order to recover work in the event of a crash…

How to Use wire:model in Laravel Livewire for Real-Time Data Binding
Limited Time Offer! For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly. Master DevOps, SRE, DevSecOps Skills! Enroll Now The wire:model directive in Laravel Livewire is used to link data in real time between the frontend (Blade templates) and the backend (Livewire components). In order to utilize wire:model…

What is Code Supply Chain Security?
Limited Time Offer! For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly. Master DevOps, SRE, DevSecOps Skills! Enroll Now What is Code Supply Chain Security? Code supply chain security involves protecting the various components, dependencies, tools, processes, and people involved in the creation, development, and deployment of software….
What is Code Security?
Limited Time Offer! For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly. Master DevOps, SRE, DevSecOps Skills! Enroll Now Code Security refers to the practice of protecting software code from vulnerabilities and threats throughout its development lifecycle. It involves implementing security measures to identify and fix vulnerabilities, ensuring…
