Limited Time Offer!
For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly.
Master DevOps, SRE, DevSecOps Skills!
Building a cloud environment without a security-first mindset is like building a house on sand. It might look great for a while, but it won’t stand up to a storm. In my decades of navigating the shifts from local servers to the vast expanse of the cloud, I have seen one truth remain constant: security is the ultimate measure of quality. If a system isn’t secure, it isn’t finished.
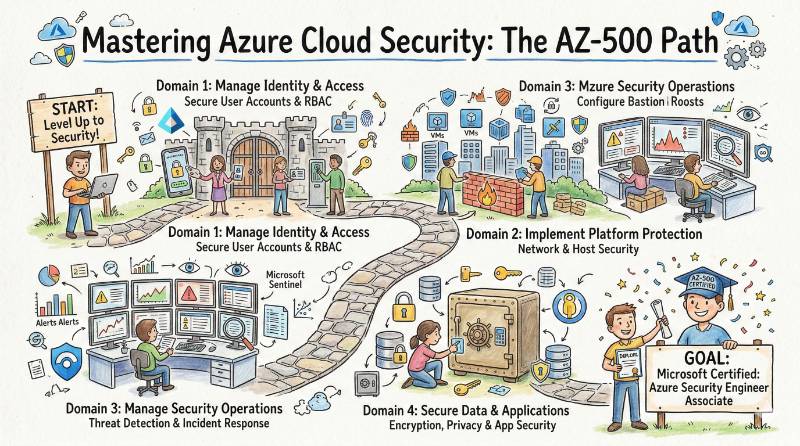
The Microsoft Azure Security Technologies (AZ-500) certification is the industry’s way of ensuring that the people building our digital world know how to protect it. This guide is written for the engineers who want to sharpen their defensive skills and the managers who need to ensure their teams are ready for modern threats. We will walk through everything from the technical core of the exam to the career paths it opens up.
Quick Look: Microsoft Azure Security Technologies (AZ-500)
Before we get into the details, let’s look at the foundational facts of this certification track.
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Security | Associate | Engineers, SREs, Developers, Managers | Azure Admin experience & Basic Networking | Identity, Network Security, Data Protection, SecOps | AZ-900 → AZ-104 → AZ-500 |
What is Microsoft Azure Security Technologies (AZ-500)?
The AZ-500 is a specialized certification that proves you can implement security controls, maintain a strong security posture, and manage identity and access across an Azure environment. It isn’t just a test of what you know; it’s a test of what you can do. It moves beyond theory and asks you to solve real-world problems involving firewalls, encryption, and threat detection.
Who should take it
This certification is designed for technology professionals who have a hand in managing cloud resources.
- Software Engineers: If you want to build apps that are secure by design, you need this knowledge.
- DevOps & Cloud Engineers: Those responsible for the “pipes” of the cloud must know how to keep them leak-proof.
- Site Reliability Engineers (SREs): Since security incidents are often the cause of downtime, SREs use these skills to ensure system stability.
- Engineering Managers: To lead effectively, you must understand the risks your team faces and the tools available to stop them.
Skills you’ll gain
Mastering this program changes how you look at the cloud. You stop seeing services as just tools and start seeing them as assets that need specific layers of protection. You will gain the ability to build a “defense-in-depth” strategy, where every layer—from the user login to the database—is guarded.
- Identity and Access: Mastering Microsoft Entra ID (Azure AD), including how to set up Multi-Factor Authentication (MFA) and Conditional Access policies.
- Platform Protection: Learning to build secure networks using Azure Firewall, Network Security Groups (NSGs), and Private Links.
- Data and Application Security: Understanding how to use Azure Key Vault for secrets and how to encrypt data so that it is useless to anyone who shouldn’t see it.
- Security Operations: Learning how to monitor your entire environment using Microsoft Sentinel and how to automate responses to security alerts.
Real-world projects you should be able to do after it
Knowledge only matters if you can use it. After completing this course, you will be ready to lead projects that directly protect your organization.
- Build a Zero-Trust Environment: Designing a system where no user or device is trusted by default, ensuring every access request is verified.
- Secure a Multi-Tier Web App: Setting up a web application where the database is completely hidden from the internet and the front end is protected by a Web Application Firewall (WAF).
- Automate Threat Response: Creating a system in Microsoft Sentinel that automatically blocks an IP address if it tries to log in too many times with a wrong password.
- Enforce Governance at Scale: Using Azure Policy to make sure that no one in the company can create an insecure resource, like an unencrypted database.
Preparation plan
Depending on your current experience, here is how you should plan your time:
- 7–14 days: This is for the experts who already use these tools daily. Focus purely on practice exams to understand how Microsoft phrases its questions and to brush up on services you might not use every day.
- 30 days: This is the ideal path for most working engineers. Spend one hour a day on the concepts and two hours on weekends doing hands-on labs in the Azure portal.
- 60 days: If you are a manager or moving from a different field, take your time. Go through the training slowly, do every lab twice, and read the official documentation for every service mentioned in the syllabus.
Common mistakes
Many talented people struggle with this exam because they treat it like a general knowledge test.
- Focusing Only on Theory: You cannot pass the AZ-500 by just reading. You must go into the portal and actually build the firewalls and set up the identity rules.
- Ignoring the “Operations” Part: Many people study identity and networking but forget about logging and monitoring. Microsoft Sentinel is a huge part of the exam.
- Skipping the Case Studies: The exam often includes long scenarios. If you don’t practice reading these carefully, you will run out of time during the actual test.
Best next certification after this
Once you have the AZ-500, your next move depends on your career goals:
- Same Track: SC-100 (Microsoft Cybersecurity Architect) – For those who want to design the big picture of security for a whole company.
- Cross-Track: AZ-400 (Designing and Implementing Microsoft DevOps Solutions) – To become a leader in DevSecOps.
- Leadership Path: AZ-305 (Designing Microsoft Azure Infrastructure Solutions) – To move into a Solutions Architect role where security is a key part of every design.
Choose Your Path: The 6 Learning Journeys
Security is the thread that connects every part of modern IT. Depending on your interest, here is how you can use the AZ-500:
- DevOps Path: Focus on “Infrastructure as Code.” Use your security knowledge to write scripts that automatically deploy secure environments.
- DevSecOps Path: This is the most direct path. You become the person who integrates security tests into the software development cycle, ensuring speed doesn’t compromise safety.
- SRE Path: Focus on reliability. Use security monitoring tools to catch errors or attacks that could cause a system outage.
- AIOps/MLOps Path: Protect your AI models. Use Azure security to ensure that the data used to train your models stays private and that the models themselves aren’t tampered with.
- DataOps Path: Focus on the data. Use your knowledge of encryption and access control to build safe data pipelines for your company’s analytics.
- FinOps Path: Secure your budget. Use Azure Policy to prevent unauthorized or expensive resources from being created, which protects the company from financial risk.
Role → Recommended Certifications Mapping
| Your Role | The Best Path Forward |
| DevOps Engineer | AZ-104 → AZ-500 → AZ-400 |
| SRE | AZ-104 → AZ-500 → AZ-700 |
| Platform Engineer | AZ-104 → AZ-500 → AZ-305 |
| Cloud Engineer | AZ-900 → AZ-104 → AZ-500 |
| Security Engineer | AZ-500 → SC-200 → SC-300 |
| Data Engineer | DP-203 → AZ-500 |
| FinOps Practitioner | AZ-900 → AZ-500 |
| Engineering Manager | AZ-900 → AZ-500 |
Top Institutions for AZ-500 Training
Finding the right place to learn is half the battle. These institutions are known for helping engineers get certified:
- DevOpsSchool: A leader in hands-on training. They focus on real-world projects and provide mentorship from industry experts like Rajesh Kumar. They are great for those who want a practical, job-ready education.
- Cotocus: They specialize in high-level cloud architecture and security, making them a great choice for teams who need to learn how to manage large-scale enterprise environments.
- Scmgalaxy: A popular community hub that offers both training and a wealth of free resources. It’s perfect for the self-starter who likes to learn through technical blogs and community discussion.
- BestDevOps: Known for their streamlined and efficient courses. They focus on the most important technical skills you need to pass the exam and do the job well.
- DevSecOpsSchool: The go-to place if you want to focus specifically on the intersection of security and automation in the development process.
- Sreschool: Focuses on the reliability side of the cloud. They help you understand how security monitoring keeps your systems running 24/7.
- Aiopsschool: Perfect for those who want to use artificial intelligence to manage security logs and threats at scale.
- Dataopsschool: Dedicated to the security of data. They teach you how to protect data as it moves through complex pipelines.
- Finopsschool: Teaches you how to use cloud security policies to manage costs and prevent financial waste in the cloud.
FAQs: Career, Strategy, and Outcome
- Is the AZ-500 exam very hard? It is considered one of the tougher associate exams because it covers a very wide range of complex services.
- How much time do I need to study? Most working professionals find that 30 to 45 days of consistent study is the best balance.
- Should I take AZ-104 before this? While not a strict rule, it is highly recommended. Knowing how to manage Azure makes learning how to secure it much easier.
- What jobs can I get with an AZ-500? Common roles include Cloud Security Engineer, Azure Administrator, and DevSecOps Specialist.
- Is this certification valued in India? Yes, India has a massive demand for cloud security experts, and the AZ-500 is a top credential for many global firms based there.
- Does it expire? It is valid for one year, but you can renew it for free through a simple online test on the Microsoft website.
- Is there coding in the exam? You don’t need to be a developer, but you should be comfortable with basic scripting (PowerShell) and reading JSON files.
- What is the passing score? You need 700 out of 1000 to pass.
- Are there labs in the exam? Sometimes. Microsoft occasionally includes performance-based tasks where you must actually configure settings in a live portal.
- Is this better than a general security cert? If you work in Azure, this is better because it teaches you specific tools you will use every day.
- Can a manager benefit from this? Absolutely. It helps you understand the technical risks and makes you a better leader for your security teams.
- What if I fail the first time? You can retake it after 24 hours. If you fail again, the waiting period increases, but don’t give up—many experts fail their first time.
FAQs: Technical and Operational
- What is Microsoft Entra ID? It is the new name for Azure Active Directory. It is the heart of identity management in Azure.
- What is the role of Azure Firewall? It is a managed security service that protects your Azure Virtual Network resources from external attacks.
- How do I manage secrets? Use Azure Key Vault. It is a secure place to store passwords, keys, and certificates so they aren’t hard-coded in your apps.
- What is Microsoft Sentinel? It is a cloud-native SIEM (Security Information and Event Management) tool that helps you find and stop threats.
- What are Managed Identities? A feature that allows your apps to connect to other Azure services without you having to manage any passwords or keys.
- What is the difference between an NSG and an ASG? An NSG filters traffic by IP and port, while an ASG allows you to group resources together for easier rule management.
- Do I need to learn KQL? Yes. Kusto Query Language (KQL) is essential for searching through logs in Azure Monitor and Sentinel.
- How does Just-In-Time (JIT) access work? It allows you to give someone admin rights only when they need them and for a limited time, reducing the risk of a breach.
Conclusion
Mastering Microsoft Azure Security Technologies is about more than just earning a certificate; it is about taking responsibility for the digital assets you manage. In my years of seeing the industry evolve, I have found that tools change, but the principles of good security—like giving people the least amount of access they need and monitoring everything—never go out of style. The AZ-500 gives you the technical depth to turn these principles into a reality. Whether you are an engineer in India or a manager leading a global team, the cloud is only as safe as the people who manage it. Take the time to master these skills, and you will not only secure your environment but also your future as a leader in the tech industry.
