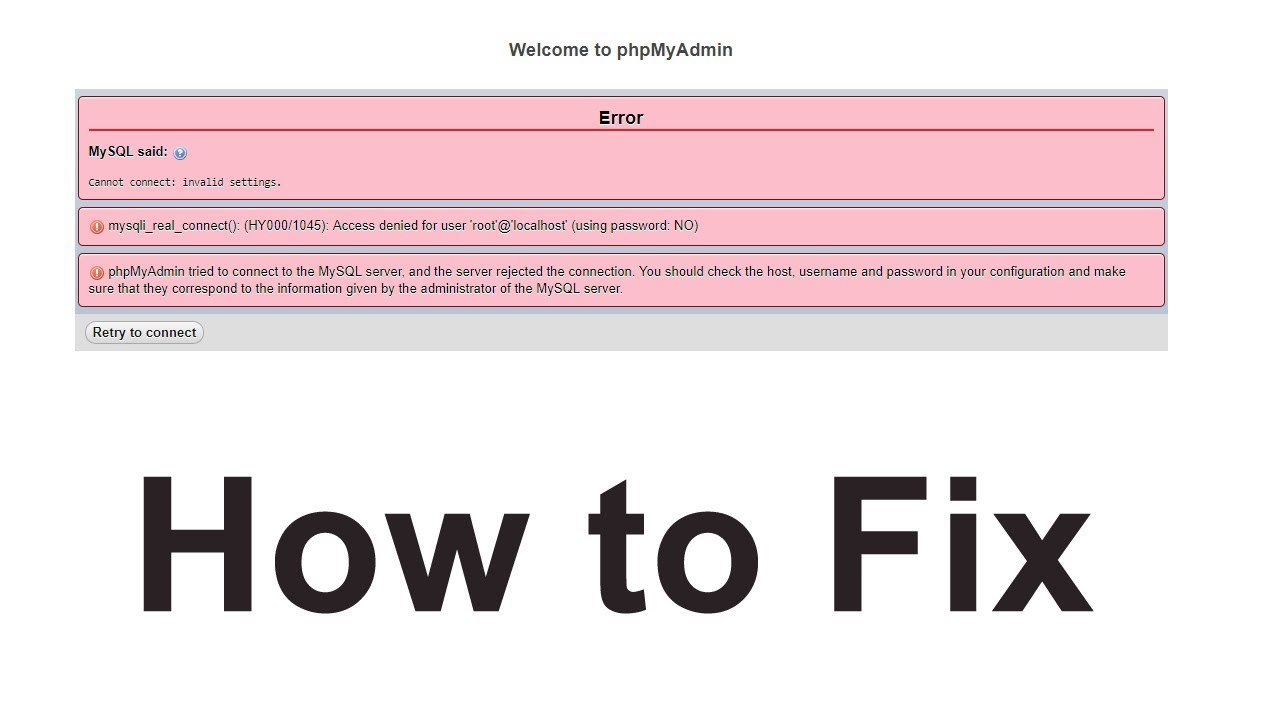
I think most of you ware facing this issue and getting stuck in this. that’s why you have came here to know about this. Why this MySQL…not running Comes? There may be several causes for MySQL’s inactivity. The following typical problems and procedures for troubleshooting them can assist you in locating and fixing the issue:…

How to do git clone without installing git in WSL (Windows Subsystem for Linux)
In this Article i m going to share the step by step guide to git clone in Windows Subsystem for Linux Ubuntu server. First of all one of the major question is raised that is installing git is necessary to git clone in Windows Subsystem for Linux Ubuntu server.Answer is – No, installing Git within the Windows…
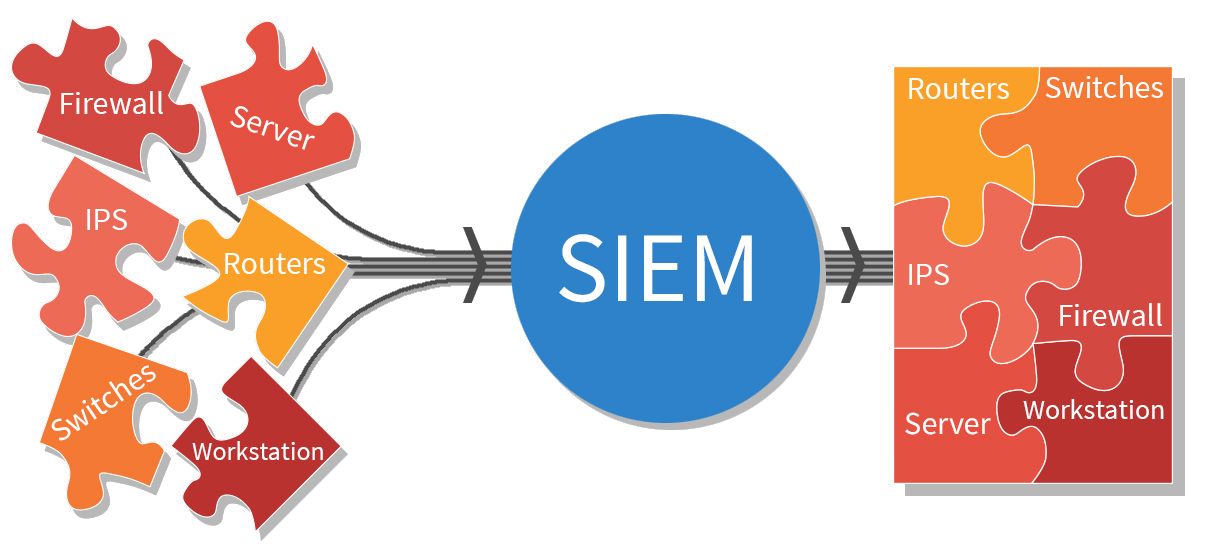
What is Security Information and Event Management (SIEM) Tools?
Combining security information management (SIM) and security event management (SEM) activities into a single security management system is known as security information and event management, or SIEM. The word “sim” in the acronym SIEM is pronounced without an e. Every SIEM system operates on the fundamental tenets of gathering pertinent data from various sources, seeing…
What is Antivirus and Antimalware Software?
Cybersecurity should be prioritized in all enterprises, large and small. If your company’s data gets hacked, the repercussions might be disastrous: you could lose a lot of data and be forced to pay large ransoms to get it back. Every 39 seconds or so, a hacker hits. Cyberattacks are rising year after year, and small…
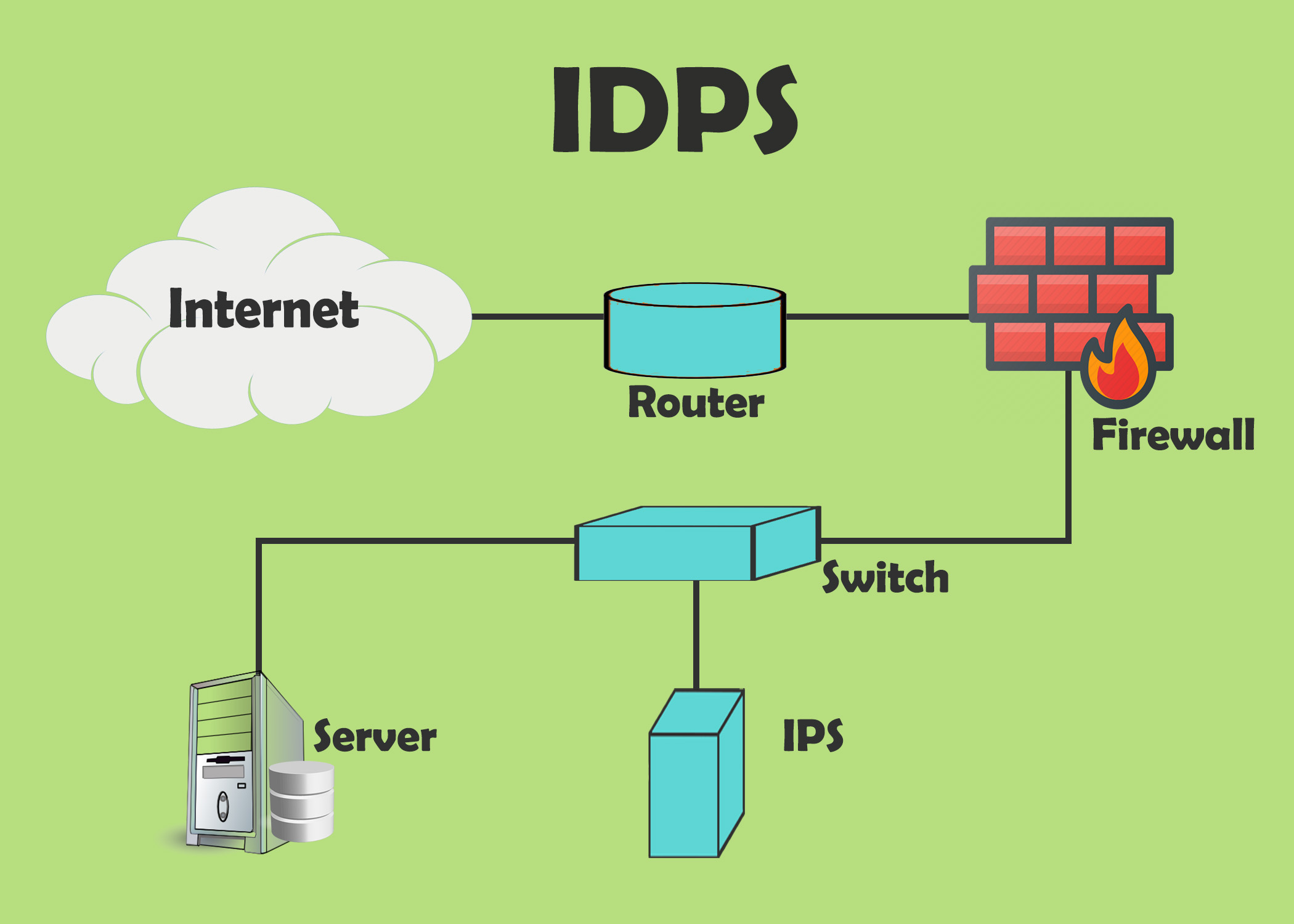
What is Intrusion Detection and Prevention Systems (IDPS)?
Security tools or software known as intrusion detection and prevention systems (IDPS) keep an eye on network traffic and systems for any suspicious behavior. They are capable of identifying a variety of dangers, such as malware, denial-of-service assaults, and illegal access attempts. By blocking harmful communication, IDPS systems may also be used to stop assaults…
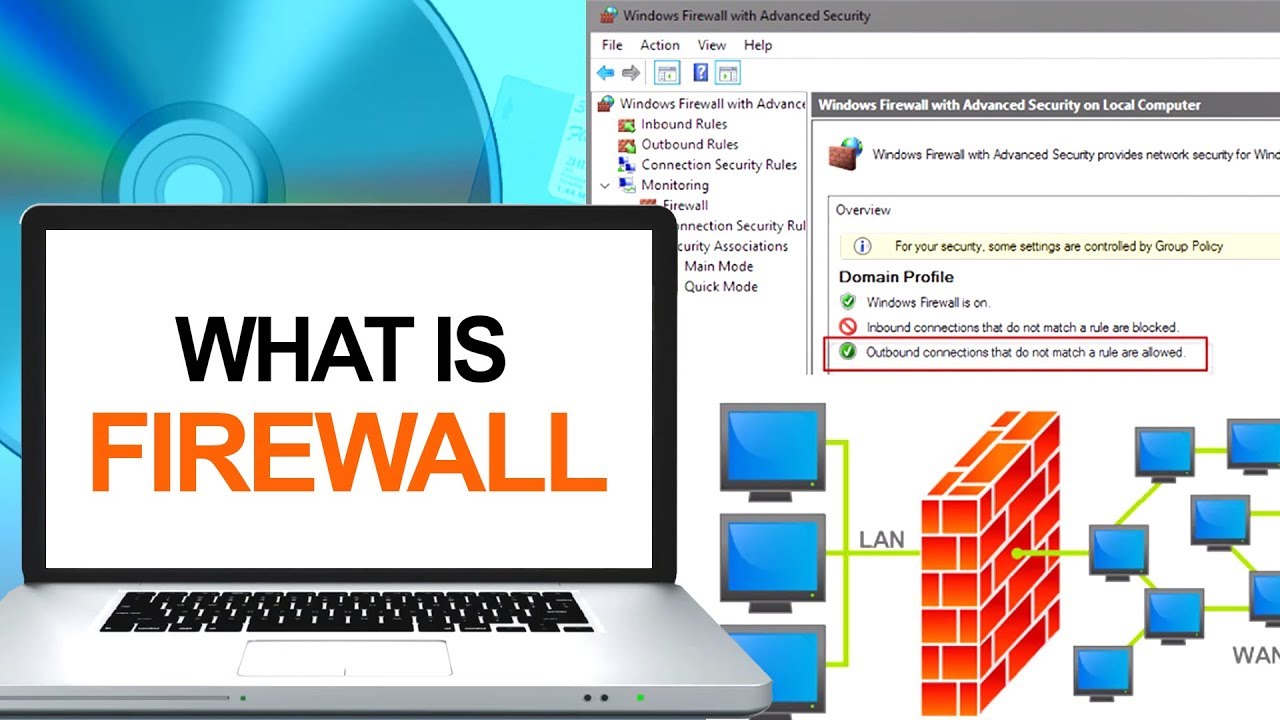
What is Firewalls?
A firewall is a type of network security device that keeps an eye on all incoming and outgoing network traffic and uses pre-established security rules to determine whether to allow or prohibit particular types of data. For more than 25 years, firewalls have served as the first line of defense in network security. They provide…
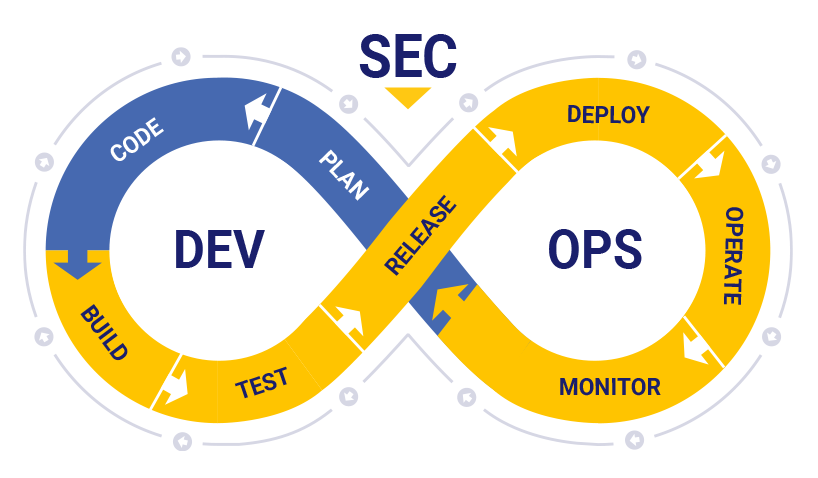
What is DevSecOps? Why? How?
Introduction DevSecOps is a set of practices that aims to integrate security (Sec) into the DevOps process. DevOps is a software development approach that emphasizes collaboration and communication between development (Dev) and IT operations (Ops) teams to automate the process of software delivery and infrastructure changes. DevSecOps extends this approach by including security as an…
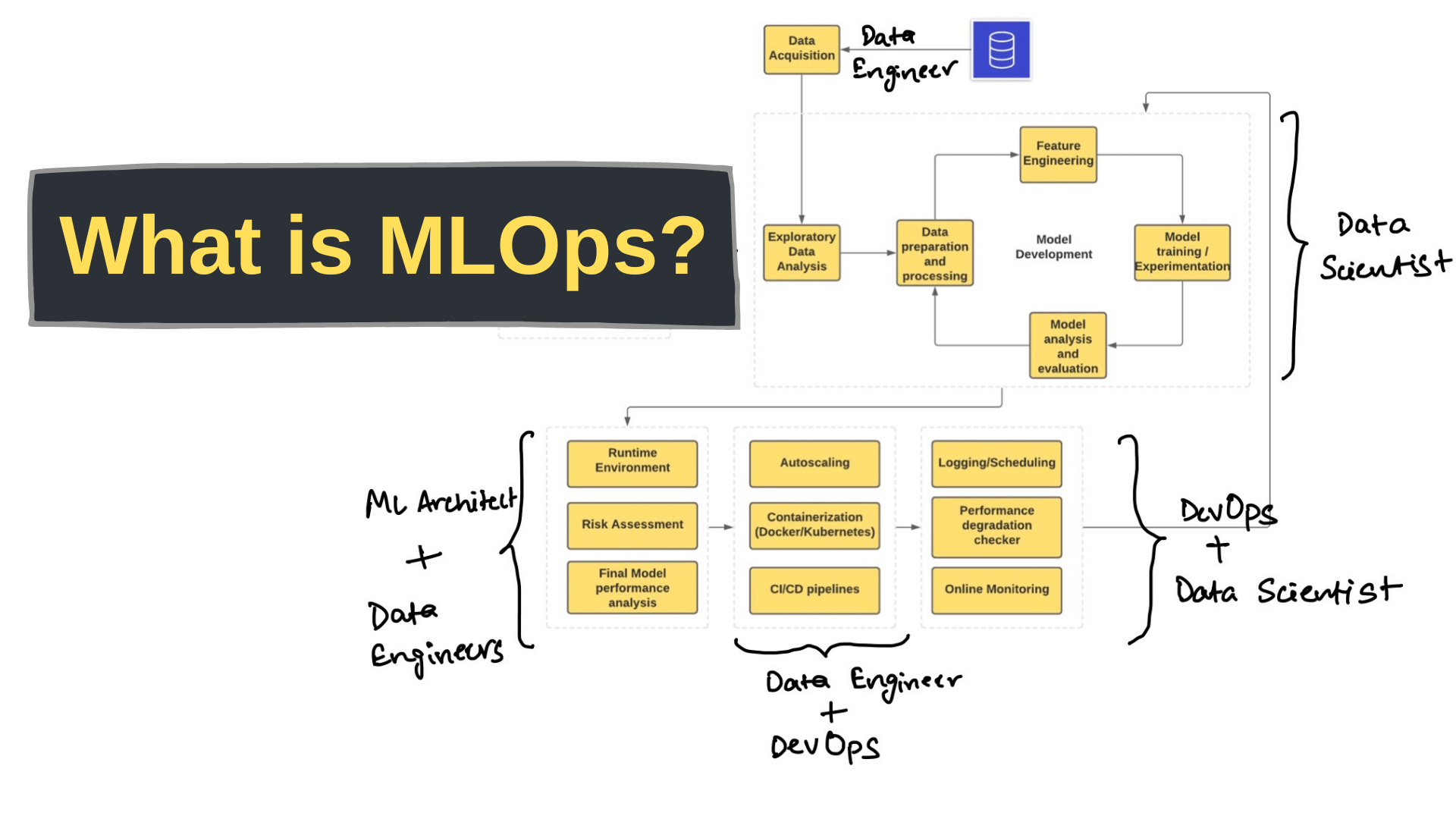
What is mlops? Why? How?
Introduction MLOps, short for Machine Learning Operations, is a set of practices and principles aimed at streamlining and automating the process of deploying, managing, and maintaining machine learning models in production. It combines aspects of software engineering and DevOps with the specific challenges and requirements of machine learning. What is mlops? MLOps, short for Machine…
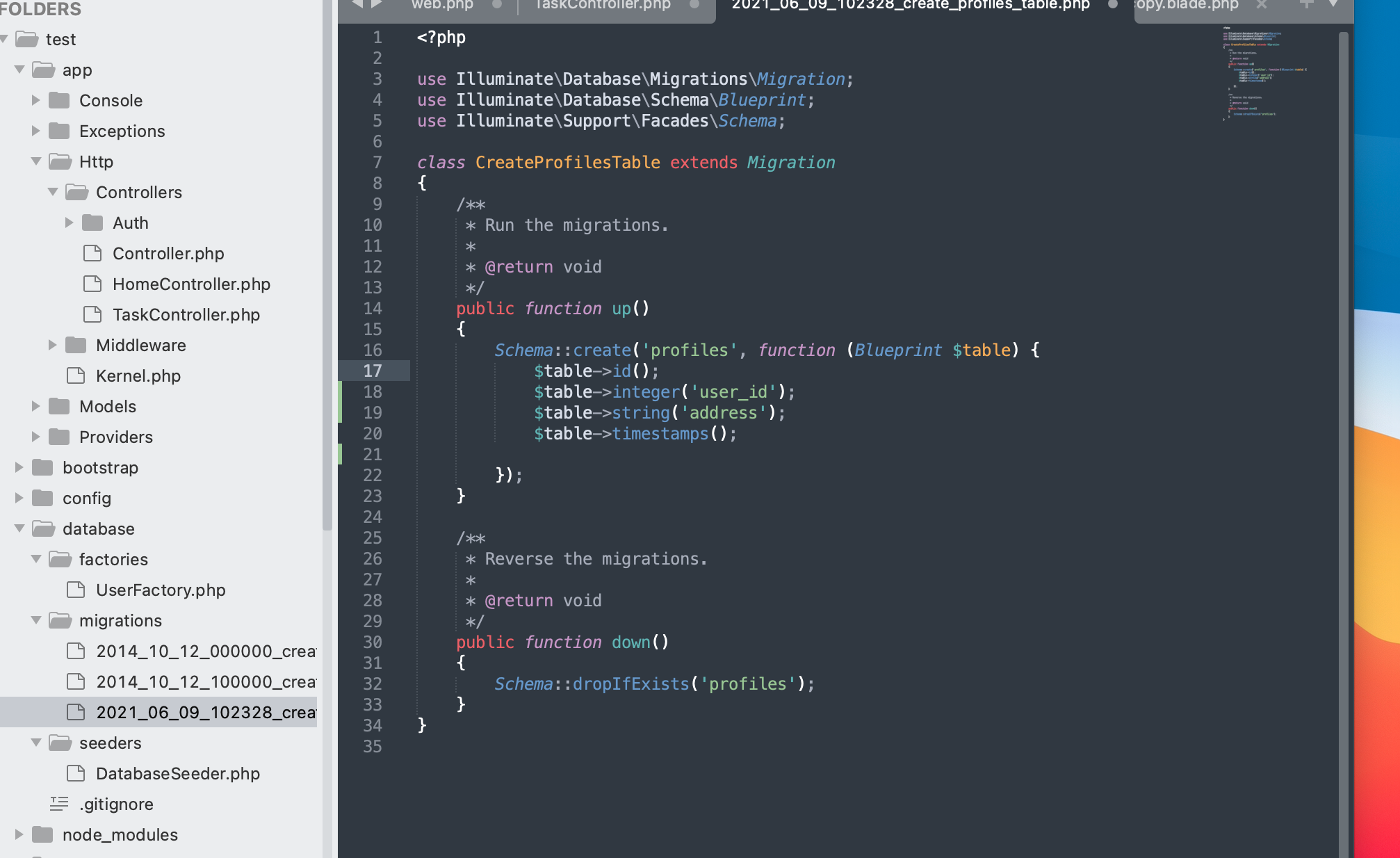
@return void Why this command is used in laravel model project?
In Laravel, the @return void comment is used in PHPDoc-style comments to indicate the return type of a method in a class, particularly in PHPDoc comments for Laravel Eloquent models. For example, consider the following Laravel Eloquent model method: Here’s what this means: So, in this example, the performAction() method is documented to not return…

What is aiops? Why & How?
Introduction AIOps, short for Artificial Intelligence for IT Operations, represents a transformative approach to managing and optimizing modern IT infrastructures. It leverages advanced machine learning and artificial intelligence techniques to automate and enhance various aspects of IT operations, including monitoring, event correlation, anomaly detection, and root cause analysis. By harnessing the power of AI, AIOps…