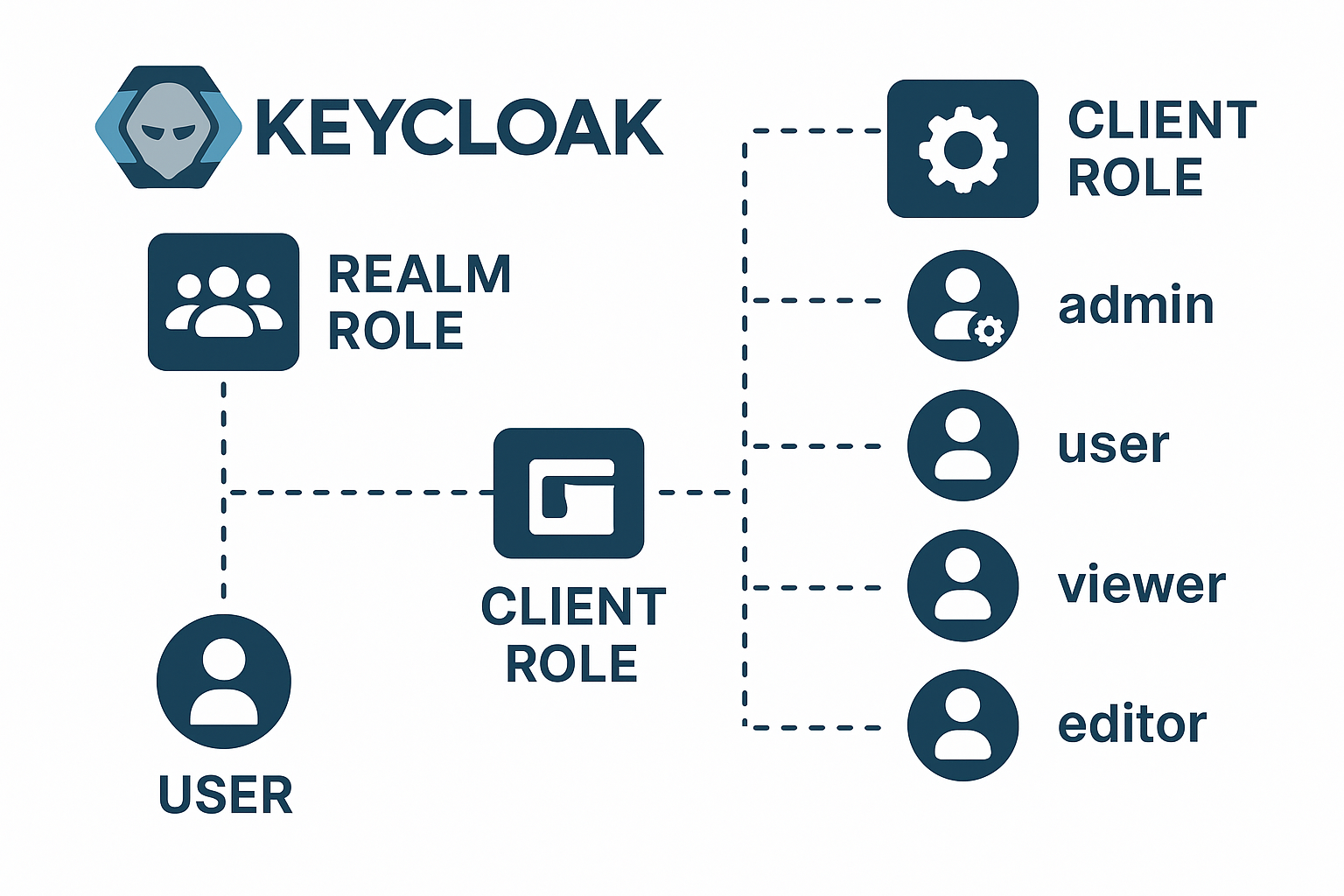
In Keycloak, clients represent applications or services (like APIs, admin dashboards, or web apps) that want to use Keycloak for authentication and authorization. Each client can have its own set of roles, called Client Roles.These roles define permissions or capabilities specific to that application. Difference Between Realm Roles and Client Roles Type Scope Assigned To…
Unlocking Infrastructure Automation: A Deep Dive into HashiCorp Certified Terraform Associate Training
In the fast-paced world of cloud computing and DevOps, managing infrastructure efficiently isn’t just a nice-to-have—it’s essential for staying competitive. Imagine provisioning servers, networks, and databases with a few lines of code, rather than endless manual clicks in a console. That’s the power of Infrastructure as Code (IaC), and at the heart of it lies…
Master the Cloud: Your Ultimate Guide to the Google Cloud Professional Cloud DevOps Engineer Certification with DevOpsSchool
The digital landscape is evolving at a breakneck pace, and the demand for professionals who can bridge the gap between development and operations in the cloud has never been higher. If you’re looking to validate your expertise and catapult your career into the stratosphere, the Google Cloud Professional Cloud DevOps Engineer certification is a golden…
The Ultimate GitOps Certification Guide
The technology landscape is in a constant state of evolution, and the practices that defined cutting-edge yesterday are the standards of today. In the realm of software delivery, GitOps has emerged as a powerful paradigm, revolutionizing how teams manage infrastructure and applications. If you’re looking to not just understand but master this methodology, the GitOps…
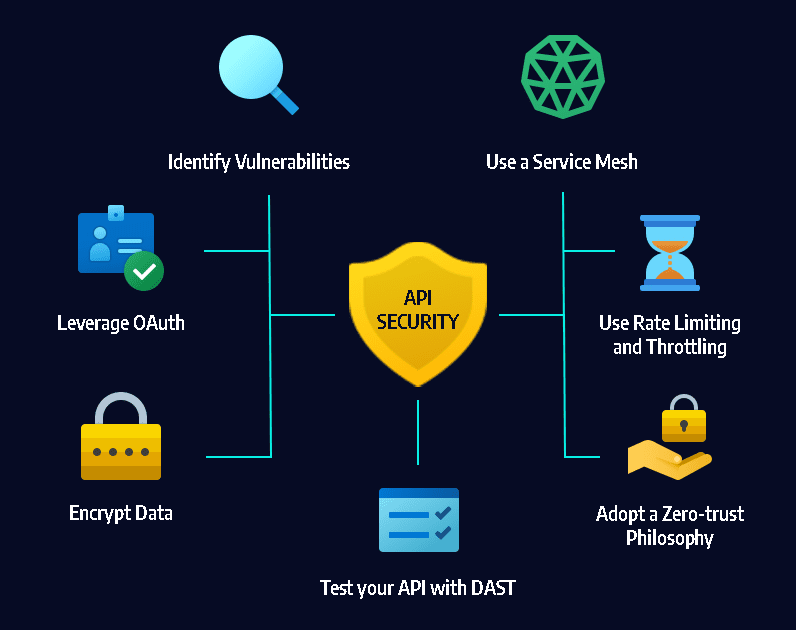
Mastering API Security: A Comprehensive Guide to Rate Limiting, CORS, Injection Attacks, CSRF, XSS and Essential Protections
Let’s break down API security further, moving from foundational principles into specific mechanisms, vulnerabilities, and protections. This will help you see not just what is done, but why and how each practice impacts the overall security of your APIs. 1. Authentication & Authorization 2. Data Encryption & Privacy 3. API Gateway & Traffic Management 4….
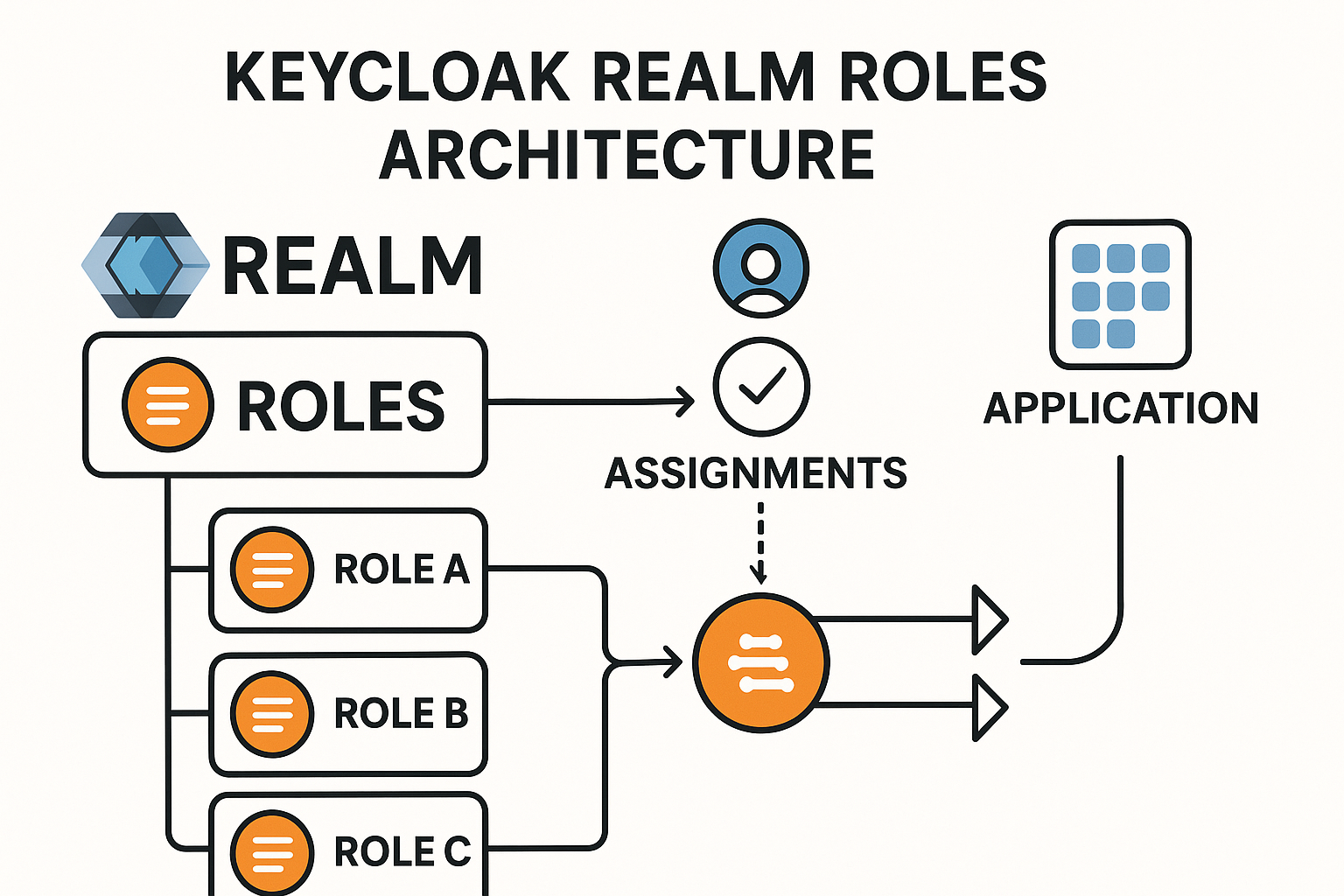
Keycloak Realm Roles: A Comprehensive Guide for Developers
Keycloak is an open-source identity and access management solution. It allows you to secure applications and services by managing users, roles, and permissions. One of the essential concepts in Keycloak is realm roles, which provide a global method for managing user permissions within a specific realm. This tutorial will walk you through the concept of…
Elevate Your DevOps Career with DevOpsSchool’s Istio & Envoy Certification
In the dynamic landscape of cloud-native technologies, managing microservices effectively is a must for any DevOps professional or cloud engineer. Service meshes like Istio, powered by the high-performance Envoy proxy, are revolutionizing how organizations handle traffic, security, and observability in Kubernetes environments. If you’re ready to elevate your expertise and stand out in the industry,…
Docker Certified Associate (DCA): The Ultimate Guide
In today’s fast-paced tech landscape, knowing how to containerize applications isn’t just an advantage—it’s a necessity. As the industry standard for containerization, Docker leads the charge, and the Docker Certified Associate (DCA) certification has become the most credible way to prove your expertise. But how do you go from understanding Docker concepts to confidently passing…
Go Fast and Safe: The DevSecOps Certification Guide
Imagine a race car built for incredible speed, but without brakes or a roll cage. That’s what modern software development can look like when DevOps speed is prioritized over security. The results are predictable: vulnerabilities, data breaches, and frantic firefighting. What if you could build the brakes and the safety features right into the engine…
DevSecOps Certification: Your Pathway to Secure DevOps
Introduction The rapid adoption of DevOps practices has transformed software delivery, emphasizing speed and automation. As this digital shift accelerates, embedding security within the development lifecycle is essential. DevSecOps addresses this imperative by integrating security controls from the outset—minimizing vulnerabilities without hindering delivery. For organizations and professionals intent on mastering this discipline, the DevSecOps Certified…