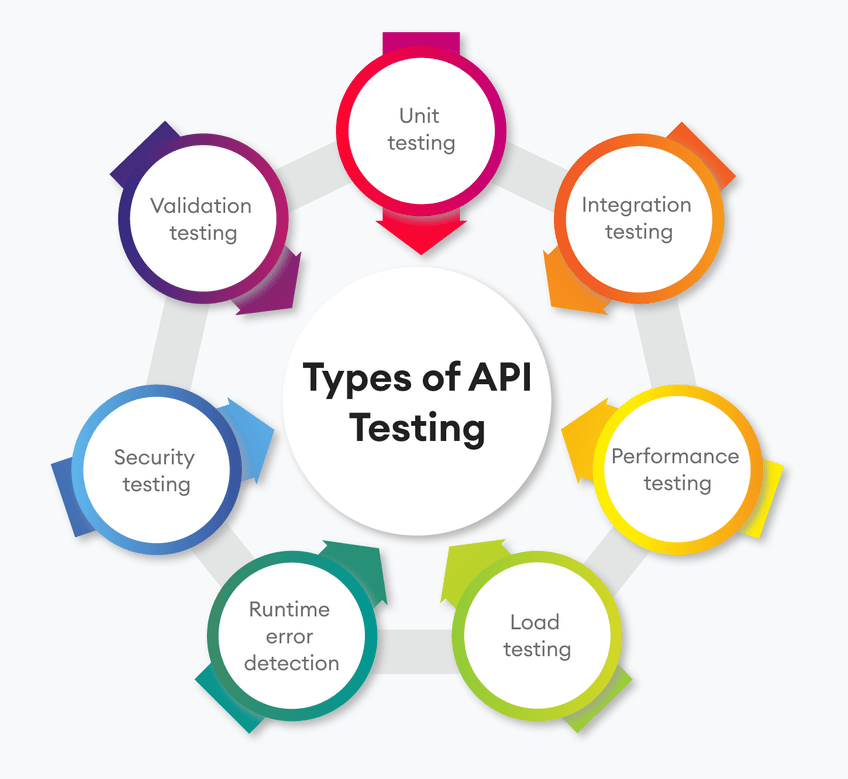
Introduction to API Testing APIs, or application programming interfaces, are now essential for smooth communication between various software systems in today’s digital environment. Ensuring the dependability, security, and performance of APIs is critical as they provide functionality and communication across applications. API testing is an essential procedure that includes confirming and evaluating an API’s numerous…
Measuring the Impact of DevOps Consulting on Your Business
The adoption of DevOps practices has become essential for organizations aiming to enhance operational efficiency, accelerate innovation, and achieve a competitive edge. Engaging with a DevOps consulting company can significantly transform your business, but how do you measure the impact of such an engagement? This comprehensive guide outlines the key metrics and benefits to consider…
What is the difference between chatgpt 3.5, 4 and 4o?
The various ChatGPT versions—3.5, 4, and 4-turbo, sometimes known as 4o—represent improvements to the design and functionalities of the device. Below is a quick summary of the variations: ChatGPT 3.5 Architecture and Model Improvements: Applications: ChatGPT 4 Architecture and Model Improvements: Applications: ChatGPT 4-turbo (4o) Architecture and Model Improvements: Applications: Key Differences and Considerations: Performance:…
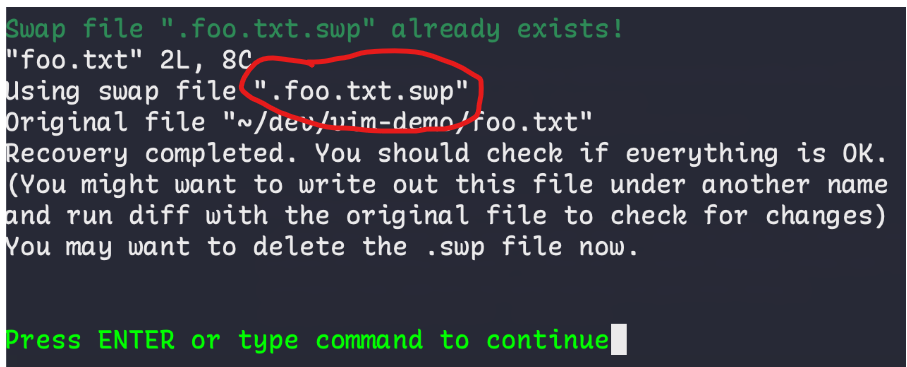
What is .swp file extension in linux?
Under Linux, swap files made with the vi or vim text editors are identified by the .swp extension. In order to recover work in the event of a crash or unintentional exit, these files are used to retain the state of a file that is being modified. Key Points About .swp Files: Managing .swp Files:…

How to Use wire:model in Laravel Livewire for Real-Time Data Binding
The wire:model directive in Laravel Livewire is used to link data in real time between the frontend (Blade templates) and the backend (Livewire components). In order to utilize wire:model properly, there are a few key elements and considerations to make: Input Fields: Text Inputs: To synchronize the component property with the input value while binding…

What is Code Supply Chain Security?
What is Code Supply Chain Security? Code supply chain security involves protecting the various components, dependencies, tools, processes, and people involved in the creation, development, and deployment of software. This type of security is critical because attackers often target vulnerabilities in the supply chain to insert malicious code, steal data, or disrupt services. Supply chain…
What is Code Security?
Code Security refers to the practice of protecting software code from vulnerabilities and threats throughout its development lifecycle. It involves implementing security measures to identify and fix vulnerabilities, ensuring that the code is robust against attacks and breaches. Secure coding practices aim to minimize the risks associated with malicious exploitation, data breaches, and other security…
What is AI-SPM (AI Security Posture Management)
What is AI-SPM? AI-SPM stands for AI Security Posture Management. It is designed to secure AI pipelines and accelerate AI adoption while maintaining protection against AI-related risks. AI-SPM provides comprehensive visibility, risk assessment, and security measures across the entire AI development lifecycle in cloud environments. It helps enforce AI security best practices by detecting misconfigurations,…

What is CWPP?
What is CWPP? A Cloud Workload Protection Platform (CWPP) is a unified security solution designed to protect workloads deployed across various cloud environments. These workloads can include servers, virtual machines (VMs), containers, and serverless functions. CWPP offers continuous threat monitoring, detection, and response capabilities to safeguard workloads throughout their lifecycle.. A Cloud Workload Protection Platform…

What is CSPM?
What is CSPM? Cloud Security Posture Management (CSPM) is a security practice and suite of tools focused on continuously monitoring and managing the security posture of an organization’s cloud environments. It helps ensure that cloud resources are configured securely, compliant with regulations, and protected from potential threats. CSPM acts as a bridge between traditional security…