Limited Time Offer!
For Less Than the Cost of a Starbucks Coffee, Access All DevOpsSchool Videos on YouTube Unlimitedly.
Master DevOps, SRE, DevSecOps Skills!
DevSecOps Use Cases in Healthcare:
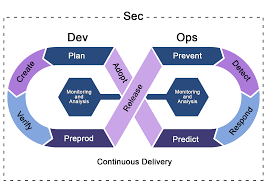
Development, Security, and Operations, or DevSecOps, incorporates security procedures into the DevOps workflow to guarantee that security is taken into account throughout the software development lifecycle. DevSecOps is essential in the healthcare industry since compliance and data security are paramount. Here are a few examples of how DevSecOps is being used in healthcare:
1. Secure Patient Data Management
Use Case: Preventing breaches and illegal access to sensitive patient data, such as medical records and personal information.
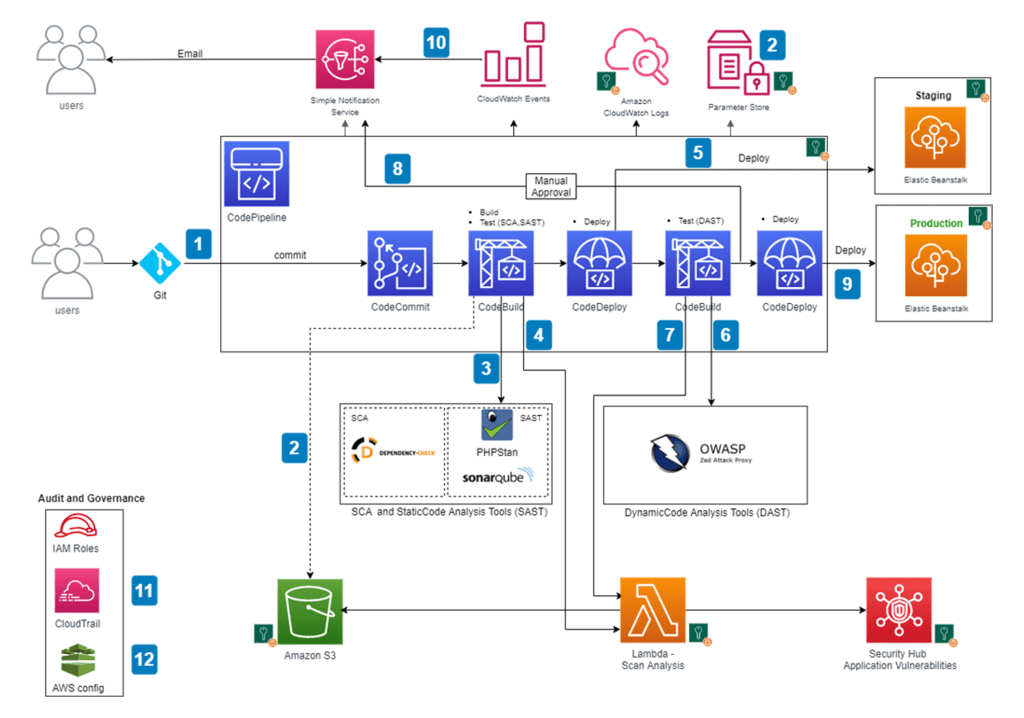
Implementation: DevSecOps ensures that security measures like encryption, access control, and regular vulnerability assessments are integrated into the software development lifecycle. Continuous monitoring and automated testing for security vulnerabilities help maintain data integrity.
2. Compliance with Regulations (HIPAA, GDPR)
Use Case: ensuring that healthcare apps adhere to legal requirements such the GDPR (General Data Protection Regulation) in Europe and the HIPAA (Health Insurance Portability and Accountability Act) in the United States.
Implementation: Automated compliance checks and audit trails included into the CI/CD pipeline are examples of DevSecOps methods. This lowers the chance of non-compliance by guaranteeing that any modifications to the code are promptly verified against regulatory standards.
3. Medical Device Software Security
Use Case:safeguarding software in medical equipment that is linked to networks and may be subject to cyberattacks.
Implementation: Secure coding techniques, frequent security testing, and ongoing software monitoring of medical device software are all part of DevSecOps processes. In doing so, security flaws are found and fixed before they may be exploited.
4. Telemedicine Security
Use Case: defending telemedicine platforms from online attacks and guaranteeing safe patient-provider interactions.
Implementation: DevSecOps makes guarantee that secure APIs, encrypted communication routes, and ongoing threat monitoring are used in the development of telemedicine apps. The DevSecOps approach includes automated vulnerability testing and regular security assessments.
5. Data Integrity in Clinical Trials
Use Case: Ensuring the integrity and confidentiality of data collected during clinical trials.
Implementation: Automated compliance checks, continuous monitoring, and secure data management protocols are examples of DevSecOps methods. This guarantees the preservation of data integrity during the trial and prompt resolution of any security vulnerabilities.
6. Incident Response and Recovery
Use Case: Quick action in the event of a security breach to reduce the disruption to medical services.
Implementation: Mechanisms for automated incident identification and response are made possible by DevSecOps. The CI/CD pipeline’s integration of security technologies enables prompt detection and fixing of security problems, guaranteeing the continuation of medical services.
7. Secure Collaboration and Data Sharing
Use Case:facilitating safe cooperation and data exchange between various medical professionals, academics, and organizations.
Implementation: DevSecOps ensures that data-sharing platforms are built with robust security features, including encryption, access controls, and secure APIs. Continuous monitoring and automated security testing are integral to maintaining the security of shared data.
8. Risk Management
Use Case: Managing and reducing the security risks associated with new healthcare software deployments.
Implementation: DevSecOps approaches include ongoing risk assessment and automated security testing within the CI/CD pipeline. This enables for early detection of possible security issues and proactive remediation prior to deployment.
9. AI and Machine Learning in Healthcare
Use Case: Protecting AI and machine learning algorithms used in healthcare for diagnosis, treatment planning, and predictive analytics.
Implementation: DevSecOps incorporates security measures into AI/ML model creation and deployment, such as secure data management, model validation, and ongoing monitoring for abnormalities or malicious activity.
10. Supply Chain Security
Use Case: Securing the software supply chain to guarantee that third-party components used in healthcare applications are not vulnerable.
Implementation: DevSecOps methods include automatic security scanning of third-party components, ongoing monitoring, and the implementation of security controls across the supply chain. This helps to detect and mitigate hazards connected with third-party applications.